The Top 20 Cyber Security Threat Strategies
Cyber security seems like a very complex issue that requires deep, and seldom available, expertise to do it right. Here is a quick checklist that our information security users have turned into a Template in CommandHound for others to use. This checklist goes after the low hanging fruit by applying the 80/20 rule.

The Top 20 Things
Here is the answer, a quick checklist of the 20 most important things you can do to begin to protect yourself, and your business, from potential information security issues:
1. Automatic Screen Lock
Make sure you turn on the automatic security lock feature on all the devices you use – laptop, desktop, tablet, and phone. Set it to anywhere between 2-5 minutes. The key test is to define an interval that best defines when your attention has shifted away from the devices onto something else.
2. Passwords
Make sure that you change your passwords often. If you can automate the forcing of all your users to change their passwords periodically, the better. Also, make sure you use strong passwords that are at least 10 characters long and combine upper and lower case letters, numbers, and special characters.
3. Train Employees
Make sure you have a regular training program for your employees to update them on the latest threats and ho to best identify them. Also, to remind them of policies and procedures and any updates.
4. Policies
Make sure you define and regularly update and communicate your IT, information security, data handling, Internet use, and all other relevant IT policies.
5. Employee and Contractor Onboarding
Make sure that you define and consistently execute an employee/contractor onboarding process that includes through background checks for anyway that will have access to your information and IT assets.
6. Employee and/or Contractor Offboarding
Just as onboarding a new employee or contractor is critical, the process of offboarding terminated employees or contractors that have finished their engagement is critical.
7. Disposal
Make sure that you define and consistently execute an IT and information disposal process that includes things like complete device destruction, memory and hard disk reformatting, and/or shredding.
8. Physical Access
Make sure you secure access to areas where important information or computing devices are stored or used. Install laptop lock cables, place servers in secured and locked locations, limit access to all areas to authorized and properly vetted personnel.
 Controlling Physical and Digital Access During Employee Onboarding and Offboarding Is Critical
Controlling Physical and Digital Access During Employee Onboarding and Offboarding Is Critical
9. Cyber Access
Make sure that the entire life cycle of a person’s access to IT resources and data is properly controlled, encrypted, and monitored. From properly conducting employee onboarding, to carefully defining who has access to what, to monitoring and logging all actions by all users while they are in the systems, to encrypting stored data and communications infrastructures, and properly executing a through employee offboarding process when necessary.
10. Backups
Make sure that all backups are encrypted especially the offsite copies.
11. Remote Access
Make sure that all remote access to anything follows proper secure channels such as using a VPN, using secure https connections, use a cell phones hot spot features instead of public Wi-Fi networks, etc.
12. Software Updates
Make sure all operating system and third-party software is updated automatically as soon as new updates or patches are available. Get in the habit of turning computers off at night to make sure updates take and to clean any residual garbage that may be lingering in memory.
13. Virus Scans
Make sure you run complete virus scans of all your devices on a regular schedule. Make sure the latest updates are incorporated as soon as they are available.
14. Email
Teach everybody proper and safe email use. Make sure everybody knows how to identify and ignore or delete suspicious emails, attachments, links, sender email addresses, etc.
15. Device Tracking
It is very important to know where your information is at all times to be able to respond and understand the severity of a potential data breach. Laptops, phones, thumb drives, hard disks, backups.
16. Real World
Make sure people learn to be aware, to identify, and to take action to address things like people or strangers that do not belong in certain areas, open doors that should be closed, screens that are on when they should be locked, or phones or tables left on desks or at the break room.
17. Experts
Make sure you use experts with the most up to date knowledge and expertise in cyber security threats, equipment, network monitoring software, and firewalls when you are setting or modifying your IT infrastructure.
18. Plan
At the end of the day, it is impossible to protect against all cyber threats. Have a well defined and tested security breach response plan or disaster recovery plan for those times when an incident actually happens.
 Cloud Computing Providers Usually Provide Best In Class Cyber Security Protections
Cloud Computing Providers Usually Provide Best In Class Cyber Security Protections
19. Cloud
Consider using a cloud computing provider if you are not there already. Cloud providers’ core mission is to maintain a safe IT environment for all their clients. Making sure that their environment is literally up-to-date and as close to bulletproof as possible is a core competency.
20. Insurance
Finally, consider getting business interruption and liability insurance to cover any potential losses directly associated with cyber security breaches.
CommandHound
CommandHound is a task management and accountability tool that is being used by information security professionals to manage their information security compliance activities.
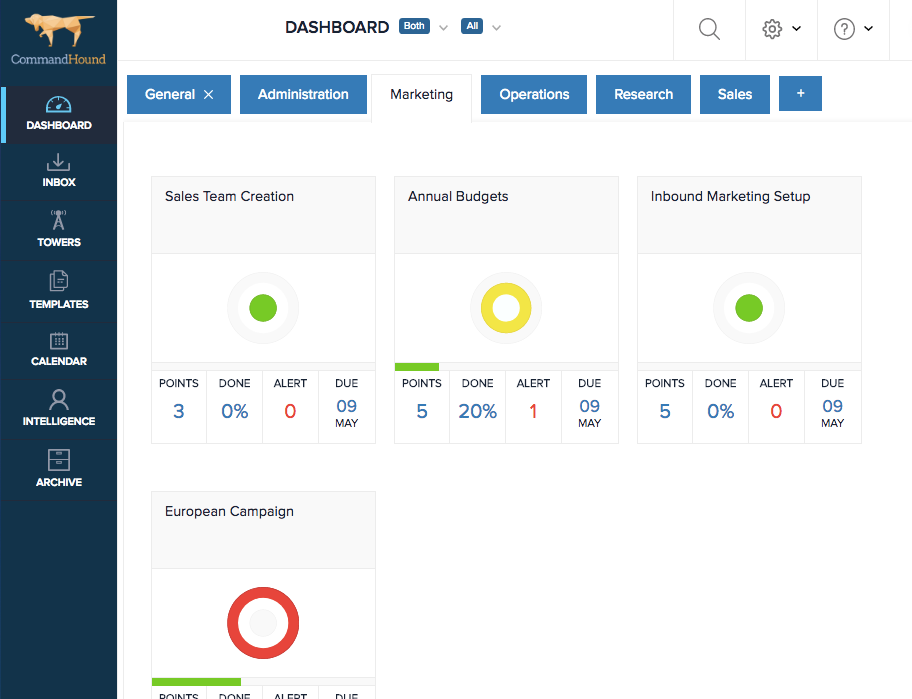
CommandHound’s Dashboard Shows Areas That Need Management Attention
CommandHound allows to define checklist like this one, assign responsibilities, due dates, escalation triggers for when thing do not get done on time, and it keeps track of people’s performance in completing what has been assigned to them to be able to drive accountability.
CommandHound’s dashboard quickly highlight areas that are falling behind and that require management’s attention.
Would you like to learn more about how CommandHound can help you address your cyber security needs?
